The time has come to set up a Data Resilience Cloud. Data resilience is different from cloud data protection, which focuses on being able to recover from attacks and stopping them from spreading. A Data Resilience Cloud doesn’t sell software or hardware. Instead, it helps you solve your security issues. The way cloud resources are used changes from day to day, which makes it hard for a typical backup system to keep up. It might need a huge increase in capacity one day, and then less the next.
With an on-premises system, the only method to adapt to changing demand is to dynamically allocate, then have a major section of the system go idle at any one time. A cloud-first approach gives businesses complete access to all the computing, networking, and storage resources they require without having to buy or manage it. They may increase capacity as needed while simultaneously lowering costs, as necessary. Organizations may get the latest and best features as a service without ever having to update or manage their infrastructure.
What is Data Resilience in Cloud?
Cloud data resilience starts with strategic alignment with key business stakeholders, planning and executing with an architecture that allows true resilience, and having a strong disaster recovery program in place as an important insurance plan for keeping your data safe. Your company’s IT system is important to how it runs day-to-day, so the cloud is more than just a place to go; it’s a way to become more efficient. If cloud technology is used properly, clients all over the world may be able to feel safer.
Resiliency is a system’s ability to get back on its feet after a failure and keep working. It’s not enough to just avoid mistakes; you also need to know how to deal with them in a way that it doesn’t cause downtime or data loss. The goal of resilience is to keep failures from happening and, if they do, to get the service back to a fully functional state after a failure. There are several types of mistakes and it’s important to have security that fits the needs of your applications.
Cloud service companies put in a lot of money so that you can run your workloads with 99.99% uptime. Machine Learning and other advanced techniques are used to look at monitoring data and predict when hardware will fail. This helps make sure the cloud service availability.
Five Essential Pillars of Cloud Security:
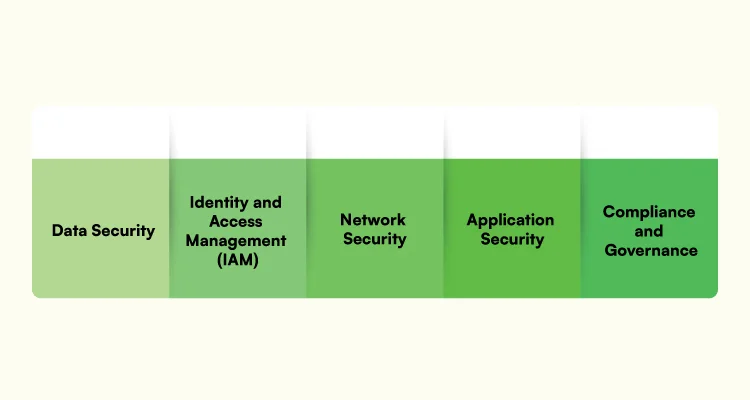
Below are the five essential pillars of cloud security. Let’s read the five pillars in detail.
- Data Security: As we all know, data is the essence of any firm, and safeguarding it against unauthorized access, loss, or corruption is critical. The first pillar of cloud security is data security, which entails adopting strong access controls, encryption technologies, and data classification policies. Sensitive information is secured from interception or unauthorized disclosure by applying encryption both at rest and in transit. Regular backup and data recovery strategies should also be in place to reduce the risk of data loss or corruption.
- Identity and Access Management (IAM): Controlling cloud resource access is critical for ensuring a secure environment. IAM is the second pillar of cloud security. IAM is the process of managing user identities, roles, and permissions in a cloud environment. Organizations can ensure that only authorized persons can access cloud resources by deploying strong authentication systems such as multi-factor authentication (MFA).
- Network Security: Network security is the third pillar of cloud security. Unauthorized access, distributed denial-of-service (DDoS) attacks, and data interception are all risks to cloud networks. Organizations should deploy strong firewall setups, intrusion detection and prevention systems (IDPS), and network segmentation to protect cloud networks. Thus, to encrypt data flows between on-premises infrastructure and cloud settings, secure connectivity methods such as virtual private networks (VPNs) and secure sockets layer (SSL) certificates should be employed. Regular network traffic monitoring and logging aid in the detection and response to any suspicious actions or potential security problems.
- Application Security: Cloud-hosted applications must be protected against common vulnerabilities and threats. Application security is the fourth pillar of cloud security. Implementing safe coding techniques, conducting frequent vulnerability assessments, and utilizing Web Application Firewalls (WAFs) to protect against typical web-based threats such as cross-site scripting (XSS) and SQL injection are all part of this.
- Compliance & Governance: Compliance and governance are the fifth and final pillars of cloud security. Cloud Service Providers (CSPs) are required to follow a variety of industry-specific legislation and standards, including GDPR, HIPAA, and PCI DSS. Organizations that use cloud services are responsible for ensuring that these regulations are followed.
Cloud Service Monitoring:
Cloud Service monitoring includes several types of monitoring. Let’s have a look into the types of monitoring.
- Database Monitoring: Because most cloud applications rely on databases, this technique examines cloud database processes, queries, availability, and consumption. This method can also track queries and data integrity, as well as monitor connections to display real-time consumption metrics. Access requests can also be logged for security reasons. An uptime detector, for example, can detect database instability and aid improve resolution response time from the precise moment a database goes down.
- Website Monitoring: A website is a collection of files that are kept locally and then sent to other computers via a network. This monitoring technique examines cloud-hosted sites’ processes, traffic, availability, and resource use.
- Virtual Networks Monitoring: This sort of monitoring develops software versions of network equipment like firewalls, routers, and load balancers. Because they are built with software, these integrated tools can provide you with a plethora of information about how they work. If one virtual router, for example, is constantly overwhelmed with traffic, the network adjusts to compensate. As a result, rather than replacing hardware, virtualized infrastructure instantly changes to maximize data flow.
- Cloud Storage Monitoring: This technique monitors storage resources and activities that are provisioned to virtual machines, services, databases, and applications at the same time. This method is frequently employed in the hosting of IaaS and SaaS solutions. Monitoring can be configured for these applications to track performance indicators, processes, users, databases, and available storage. It gives data to assist you in focusing on valuable features or fixing faults that interfere with functionality.
- Virtual Machines Monitoring: This method simulates a computer within a computer by using virtualization technology and virtual machines. In IaaS, it is typically scaled out as a virtual server hosting multiple virtual desktops. A monitoring application may keep track of each machine’s users, traffic, and status. You receive the advantages of traditional IT infrastructure monitoring as well as the advantages of cloud monitoring solutions.
Best Cloud Compliance Practices:

There are numerous best practices you can implement to help fulfill regulatory standards, but the following are especially beneficial to attaining data compliance in the cloud:
- Encryption: You should begin by encrypting the data that is in danger, both at rest and in transit. Your data, however, is only as secure as the keys you employ to encrypt it. As a result, you must also maintain strong key management practices.
- Privacy by Default: Privacy should be baked into system architecture and processing activities by default. This will make it much easier to comply with any data protection rule or standard.
- Principle of least privilege: Users should be granted access to only the data and resources they require to perform their jobs. This reduces the danger of compromise by both internal and external threat actors. It will also help you demonstrate that you are taking adequate steps to meet compliance standards.
- Zero Trust: You should always implement tight authentication, authorization, and monitoring of all users, endpoints, and apps that use your network.
- Well-architected Frameworks: You can use modular frameworks published by leading cloud vendors like AWS, Microsoft Azure, and Google Cloud Platform to guide customers through a set of guiding principles for building resilient, secure, and highly optimized workloads on their platforms.
Data Recovery Strategies:
Listed down are the major data recovery strategies in detail and
Conduct an Objective Review of Existing Legacy Systems:
Examine current legacy systems objectively before developing backup and data recovery strategies (or employing the 3-2-1 approach). Identify gaps in your organization’s digital environment’s systems, workloads, data storage, and apps. Consider moving fewer sensitive data offshore and to the cloud; for many firms, this is the first typical step in their path to the cloud. Leveraging existing on-premises solutions and cloud-based options provides businesses with a platform that allows for growth and scalability, ensuring the success of your backup plan from the start.
Implement a Data Backup Strategy of 3-2-1-1-0:
A backup strategy is essential for any thorough business continuity plan. Using a single data backup source to secure your data against deletion, disaster, and corruption is insufficient. A 3-2-1-1-0 can assist secure company assets by utilizing diverse backup techniques.
- Maintain three copies of data: keep the original data copy as well as at least two backups in case one or more are lost.
- Use two different types of storage: diversifying storage systems can assist a corporation protect itself in the case of a data failure. If data is saved on an internal hard drive, for example, use a secondary device such as an external drive or a cloud source.
- Maintain only one duplicate of data offsite: Keeping two or more copies in the same area can be disastrous in the event of a natural disaster. A reliable protection approach is to keep one copy offshore.
Run Backup and Recovery Tests on a Regular Basis:
Many organizations may conduct backup tests on a regular or semi-annual basis. However, depending on the scale of the company, even relatively occasional occurrences may not be enough to defend against potential data losses.
Companies should use this chance to conduct testing to identify flaws and make necessary fixes. If files are corrupted or compromised, businesses will be able to identify and repair issues before the data is backed up.
Data that changes often should be tested more frequently. When installing new apps or software on computers, tests and restores should be performed more often. In the event of an emergency or unforeseen event, disaster recovery plans should be examined and changed as appropriate.
Keep Policies & Procedures Documented:
Data backup plans are set techniques for copying and backing up business applications to ensure recoverability in the case of a disaster. If a company experiences a shutdown or disruption, carefully established data backup policies and procedures, as well as chain of command communication standards, can assist firms in acting quickly.
Because of the ever-increasing risk of cyber threats, all businesses should have up-to-date data recovery strategies and standardized disaster response plans. In extreme cases, data loss can lead to financial ruin and the closure of a corporation.
Cuneiform may strengthen an organization’s cyber, data, and operational resilience without any hardware, software, or related complexity by leveraging the public cloud’s ease, scalability, and security.
Cuneiform Consulting Pvt. Ltd., a cloud computing services provider, is well organized and prepared for data resilience in the cloud. We also adhere to cloud security concerns and assure the safety of your data in the cloud.